While ERC-7265 standardizes onchain circuit breakers, the real innovation lies in intelligent monitoring that acts as an external circuit breaker, catching attacks within seconds and preventing billions in losses before they happen.
The Evolution: Static code protections → Real-time behavioral monitoring → Predictive threat prevention
Here's a super useful talk about smart contract circuit breakers from Morgan Weaver (OpenZeppelin) at the Secureum Trust X event.
The misconception: circuit breakers vs. monitoring
Most developers think circuit breakers are just smart contract functions - a pause() button activated when thresholds are breached. But that's only half the story.
Traditional view:
Reality: The real circuit breaker is the monitoring system that detects the anomaly, analyzes the threat, and triggers the response - often before the onchain mechanism even activates.
The anatomy of modern circuit breaker systems
Layer 1: Onchain circuit breakers
These are the standardized mechanisms built into smart contracts themselves, like the proposed ERC-7265 standard.
ERC-7265 circuit breaker mechanics:
- Threshold-based triggers: Halt outflows when withdrawals exceed predefined limits
- Customizable responses: Either revert transactions or delay settlement
- Protocol-agnostic design: Works across different DeFi protocols
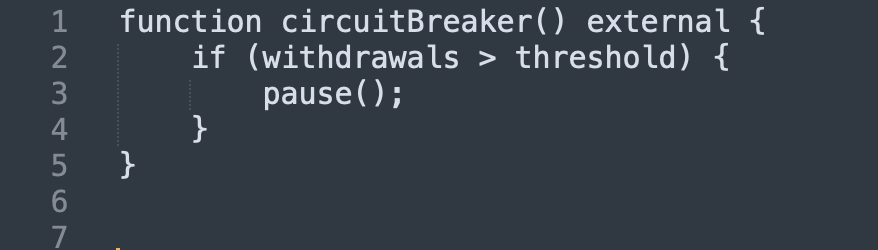
Example Implementation:

The Limitation: onchain circuit breakers are reactive - they respond after anomalous behavior has already begun.
Layer 2: Real-time monitoring as circuit breakers
This is where the real innovation happens. Monitoring systems act as external circuit breakers by:
- Detecting patterns before they become problems
- Triggering alerts in seconds, not minutes
- Enabling proactive response before significant losses
- Providing context that onchain mechanisms can't
How monitoring functions as a circuit breaker
1. Pattern recognition circuit breakers
Real-time monitoring systems analyze transaction patterns to identify potential attacks:
Flash loan attack detection:
- Normal Pattern: Small borrows → Normal repayment
- Attack Pattern: $100M+ borrow → Complex arbitrage → Partial repayment
- Monitoring Response: Alert in 15 seconds → Manual review → Block if necessary
- The Advantage: Catches attacks that stay within individual protocol limits but are clearly malicious when viewed holistically.
2. Behavioral anomaly circuit breakers
Instead of just watching numbers, these systems analyze behavior:
Normal user behavior:
- Gradual position building
- Reasonable gas fees
- Standard interaction patterns
Attack behavior:
- Sudden large transactions
- Complex multi-hop operations
- Unusual contract interactions
- MEV-like transaction timing
Real-Time response:
- Anomaly Detected → Risk Scoring → Threshold Exceeded → Circuit Breaker Activated
Time to response: 30-60 seconds vs. 10+ minutes for manual detection
3. Cross-Protocol circuit breakers
Single-protocol circuit breakers miss systemic attacks. Real-time monitoring provides:
Cross-Chain correlation:
- Same attacker addresses across networks
- Coordinated attacks on multiple protocols
- Bridge manipulation patterns
Ecosystem-Wide protection:
- Detection of attack campaigns before they spread
- Early warning systems for similar protocols
- Coordinated response mechanisms
How monitoring could have prevented recent major exploits
1 - The Resupply attack ($9.6M) - June 2025
What happened: Donation attack exploited empty vault to manipulate exchange rates Traditional circuit breaker: Would only trigger after withdrawals exceeded thresholds.
Monitoring circuit breaker would have caught:
- Unusual donation patterns to new vaults
- Extreme share price inflation in real-time
- Minimal collateral backing massive loans
Result: Attack stopped in 2 minutes vs. 90 minutes of actual drainage
2 - The Arcadia finance exploit ($3.5M) - July 2025
What happened: Circuit breaker gaming + malicious router injection
Traditional circuit breaker: Was actively disabled by attacker's strategy
Monitoring circuit breaker would have detected:
- Suspicious contract deployment patterns (bait attack)
- Non-DEX router addresses in swap operations
- Coordinated multi-day attack preparation
Result: $3.4M saved through early pattern detection
3 - The BigONE exchange hack ($27M) - July 2025
What happened: Supply chain attack compromised hot wallet logic Traditional circuit breaker: Couldn't detect compromised third-party software
Monitoring circuit breaker would have identified:
- Abnormal hot wallet withdrawal patterns
- Unusual cross-chain coordination
- Behavioral deviations in operational systems
Result: Losses limited to under $1M through rapid anomaly detection
The technical architecture of monitoring circuit breakers
Level 1: Monitoring alerts (0-30 seconds)
- Detect unusual patterns
- Generate risk scores
- Alert security teams
Level 2: Automated response (30-60 seconds)
- Rate limiting suspicious addresses
- Temporary transaction delays
- Protocol notifications
Level 3: Emergency activation (60-120 seconds)
- Trigger onchain circuit breakers
- Coordinate cross-protocol response
- Implement emergency pauses
Modern monitoring circuit breakers incorporate:
- Historical attack data for pattern matching
- Cross-protocol threat intelligence
- Real-time vulnerability assessments
- Predictive modeling for emerging threats
Regulators increasingly view monitoring circuit breakers as:
- Due diligence requirements for DeFi protocols
- Risk management standards for institutional participation
- Consumer protection measures for retail users
- Systemic risk mitigation for the broader financial system
Circuit breakers aren't just code - they're systems:
- Onchain mechanisms provide last-line defense
- Real-time monitoring enables proactive protection
- Predictive analytics prevent attacks before they start
- Coordinated response protects entire ecosystems
Important takeaway to note:
- Deploy monitoring before you need it - attacks happen without warning
- Integrate multiple monitoring sources for comprehensive coverage
- Plan graduated responses to balance security and usability
- Prepare for false positives with override mechanisms
Conclusion
Circuit breakers in smart contracts aren't just emergency pause buttons - they're comprehensive monitoring systems that detect, analyze, and respond to threats in real-time. While ERC-7265 standardizes onchain protections, the real innovation lies in intelligent monitoring that acts as an external circuit breaker.
The future belongs to protocols that don't just build with security in mind - they build with monitoring as core infrastructure.
At Guardrail, we provide comprehensive real-time monitoring that acts as an external circuit breaker for your protocol. Our systems detect threats in seconds, not minutes, and have prevented millions in potential losses.
Contact us to discuss implementing monitoring circuit breakers for your protocol.
.png)
.png)



